Blockchain is ideal in situations where settlements need to be instant and systems exceptionally efficient, and it has been proposed as a way to secure states against cyberattacks. Recently it is considered one of the most innovative and potentially useful technologies around. That is all well and good, but can we trust it? Is blockchain as secure as it is cracked up to be?
Technologies, and especially those as spectacular as blockchain, are not (and should not) be taken on faith. Indeed, any slip-up, any gap in the system or failure to fend off hackers will (with the help of a hysterical mass media) kill them.
Blockchain is steadily evolving. Right now, it is being tested in the field, and generating great expectations. This huge interest coming from industry and state governments is due, in part, from the promise made to the world by its authors: “We are giving you a system whose protections are unmatched.”
But, are they? The technology is very new and, as such, will experience teething problems. That must be understood. To decide whether it is truly secure – and will therefore establish itself in the mass market – we must first distance ourselves from the hype and frenzy over the exchange rates of the bitcoin and other cryptocurrencies.
Secure by nature
The security of blockchain results from the fundamental premises assumed in its development and embedded deep in its architecture. I am referring to the inviolability of transaction history, decentralization and the principle of cryptographic encryption – all of which translate to a high level of transaction security. (I have written about other aspects of blockchain many times, most recently here.)
Briefly, blockchain is a public ledger of transactions recorded in chronological order. Each transaction is entered in a chain of the so-called blocks. These are created based on information encrypted in previous transactions. Anyone wishing to modify the record (perhaps to the disadvantage of others) would have to change all previous records down the entire chain or alter all previous blocks or at least most of its copies. But, to do that, they would need the consent of the other users, as blockchain is a consensus-based system. Only after a specified majority (51% or other agreed) of the users (measured in terms of the computational power of new block mines) greenlight a modification can it be permanently entered in the register. If all goes well, it is confirmed in a “proof of work”: a set of complex calculations which result in the creation of a new block. The list of verified transactions is created through communications among the nodes (users), each of whom keeps a copy of the ledger and shares any new information with the other nodes.
It is, in effect, a giant jigsaw puzzle; you can’t put it together unless and until each successive piece fits with the ones laid down before. The pieces that do not fit are rejected, i.e., denied entry into the register. There is no ledger guardian, no transactional middleman. Everything that takes place within the ledger is beyond the reach of third parties, be they individuals or institutional intermediaries.By its very definition, this peer-to-peer technology is based on the premise of direct intercourse among users.
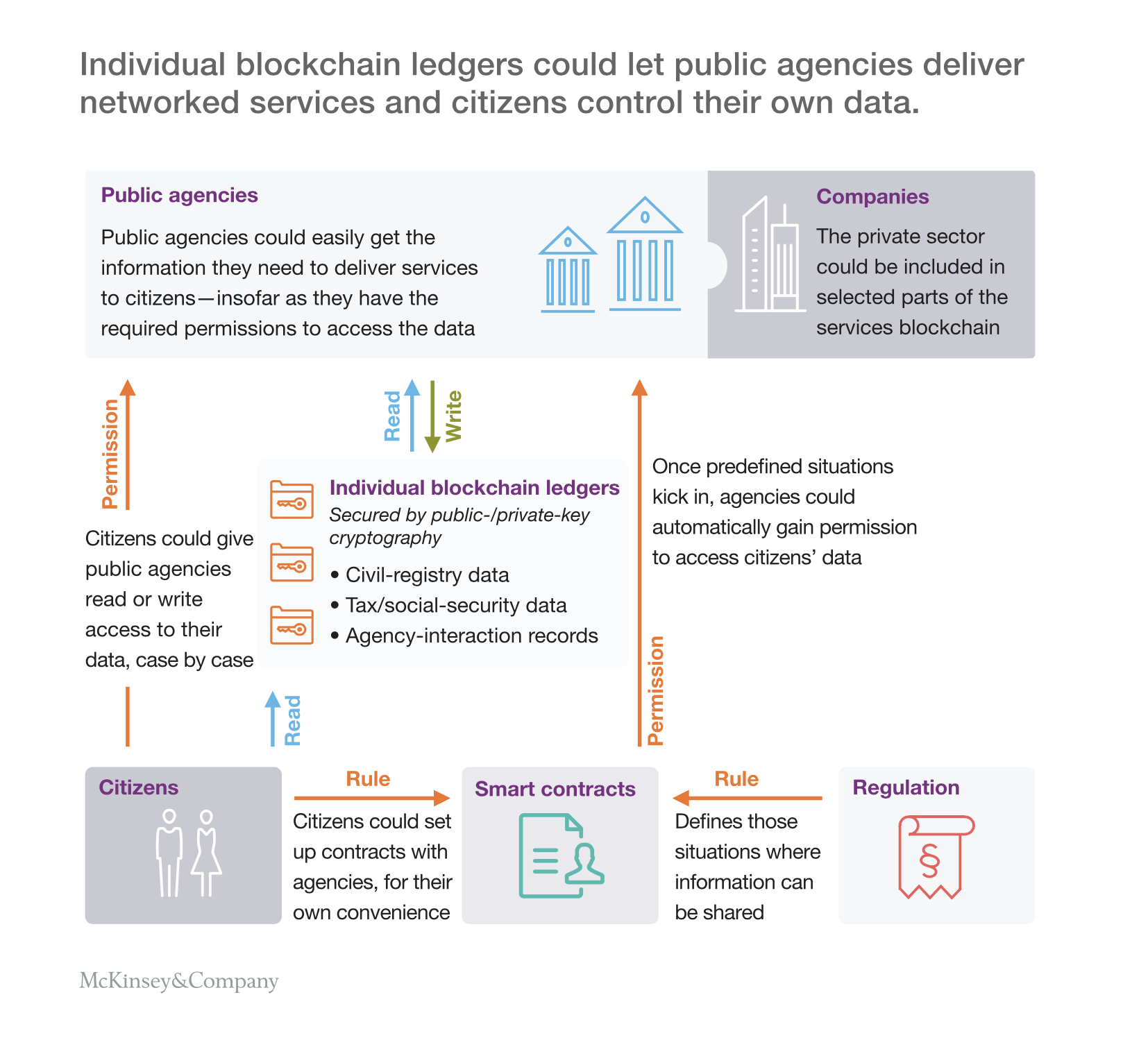
Picture 1. In certain situations, smart contracts could expose certain information to designated agencies if predefined conditions are met.Source: McKinsey
Estonia already believes
So, blockchain is a multi-level security system: records depend on history, user consensus is required, users interact directly. As a result, what has only recently been a theoretical construct has now taken concrete shape and is successfully selling itself to industry, one sector after another. The technology supports cryptocurrency markets; its diverse versions are being tested by banks, fintechs, the energy industry and health care organizations. Blockchain has become synonymous with cybersecurity. Interest has also been expressed by states which see it as a possible protection against cyberattacks. Estonia, for instance, has recently resolved to adopt a system that relies on blockchain to allow its citizens to vote, file their tax returns and pay their taxesonline. Experts believe the Estonian system cannot be hacked, at least without leaving an easy to follow trail that would, of course, discourage hackers.
Quantum monsters
By all indications, blockchain’s popularity is fluctuating in lockstep with the cryptocurrency market. In the popular imagination, blockchain isbitcoin and other cryptocurrencies. Reports on hack attacks on cryptocurrency exchanges, and sensational news on cryptocurrency theft, have eroded people’s confidence, making them wonder if blockchain is as secure as its advocates and promoters claim.
Even the optimism of those who trust it has been dented by reports on the capabilities of quantum computers. Once blockchain falls into unauthorized hands, quantum machines(as I have explained in greater detail here) could pose a threat to the cryptographic protections of the public key (which, after all, is the core of blockchain) by hacking it and replicating it, which would compromise the security of information exchange among users.
In a nutshell, a blockchain network user uses the so-called public key, which is generally available, to encrypt specific information before it is passed on. To decrypt such information, its recipient would use a private key: a unique, counterfeit-proof string of characters generated by an algorithm and available solely to private key holders.
The chance of generating a private key by examining the public one is virtually nil. It would take billions of years to complete such decryption.However, what an ordinary computer cannot do is within the reach of quantum machines, whose computing capacities – thanks to its freedom from binary bondage – are astonishing, and a hacker with a quantum machine could (theoretically) reproduce a public key character string.
And, even without the quantum monster…
Another threat – more pressing today than worrying about quantum machines in the hands of hackers – is the loss or theft of the private key. This usually occurs when it is stored on a computer connected to the internet. Once a key has been stolen, the rightful owner has no recourse. No transaction concluded by means of a stolen private key can be distinguished from one conducted legally.
Now, cases like this can hardly be attributed to a security flaw in the blockchain itself. The problem is user carelessness. But this gives rise to the dilemma of whether and under what circumstances one should cancel verified transactions if they are believed to result from theft. The inviolability and irreversibility of transactions is one of blockchain’s main pillars, its value proposition, if you will. Repeal or change this rule, and users could lose their confidence in the system’s impartiality.
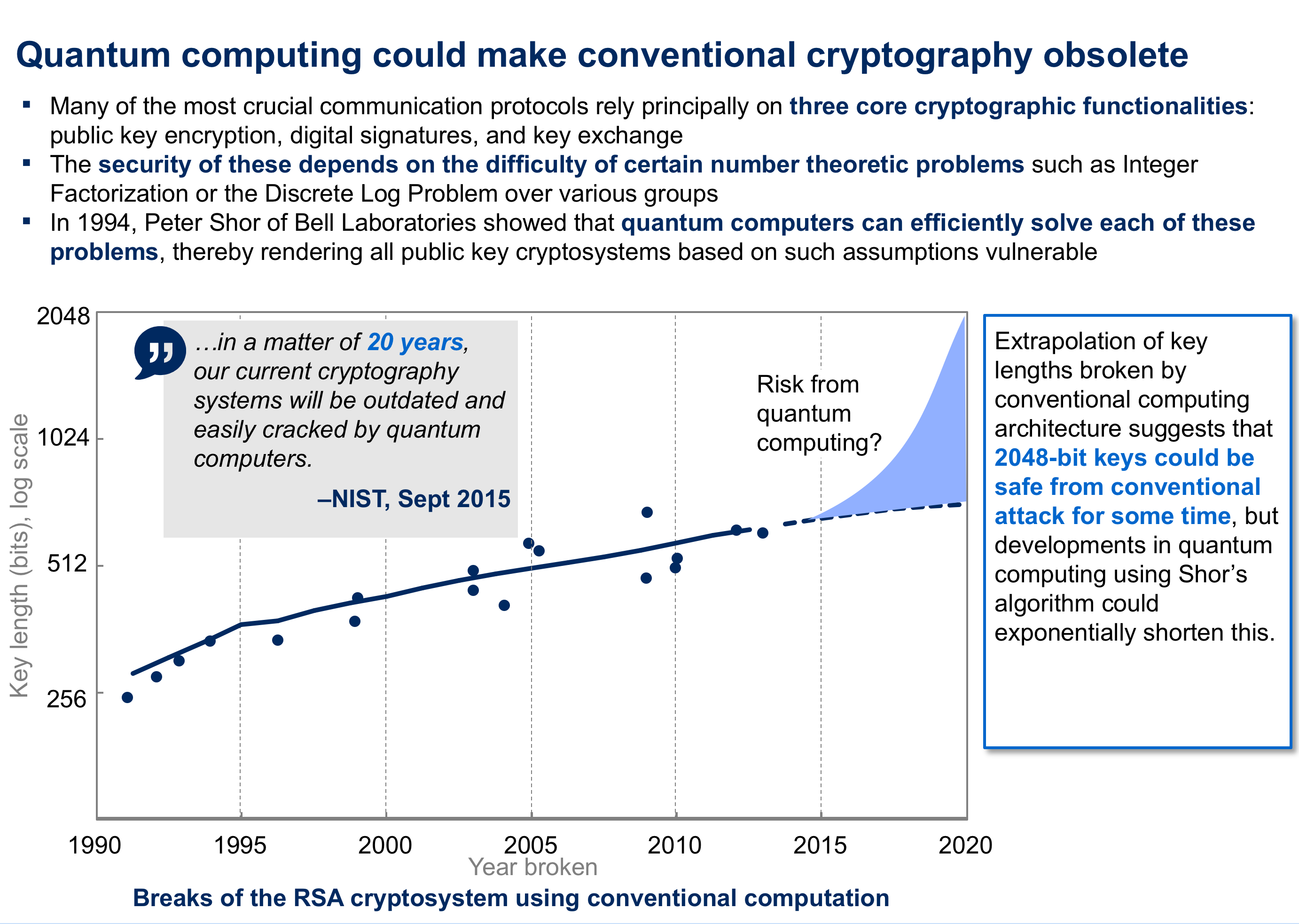
Picture 2. Quantum computing could make conventional cryptography obsolete. Source: McKisney
Teething pains
These challenges to 100% blockchain security result from its relative newness. The IT solutions, codes and protections on which it relies are only beginning to blaze new technological trails. The consensus is that distributed data is much harder to hack than data stored on a single machine. The rule requiring multiple parties to consent to changes sounds equally convincing. However, the actual practice is more complicated. This applies also to areas that seem immune to trouble, such as encryption. Much depends on the policies adopted by private blockchain network operators.
Nevertheless, I am certain that despite sensational reports on the hacking of cryptocurrency exchanges, we are witnessing the dawn of a breakthrough technologythat is also incredibly secure. The changes it will bring to financial settlement and transaction markets will be as radical as the transformation the internet wrought in communications.
. . .
Works cited
Steve Cheng, Matthias Daub, Axel Domeyer, and Martin Lundqvist,Using blockchain to improve data management in the public sector,McKinsey Global Institute, link, 2018.
Nolan Bauerle, What is Blockchain Technology,CoinDesk, link, 2017.
Martin Lundqvist and Peter Braad Olesen,Digitizing the delivery of government services, McKinsey Global Institute, link, 2017.
Estonian blockchain technology. What is blockchain technology and how is it related to e-Estonia,e-Estonia, link, 2017.
The CEO of D-Wave Systems, Vern Brownell, The growing potential of quantum computing, McKinsey Global Institute, link, 2016.
. . .
Related articles
– Blockchain poised to shake up our lives
– Will quantum computers doom the blockchain?
– Why do we care about blockchain technology?
– Will a basic income guarantee be necessary when machines take our jobs?
– Machine Learning. Computers coming of age
– What a machine will think when it looks us in the eye?
–Blockchain – the ultimate financial crash








Tom Jonezz
The killer app for blockchain is money. Not bananas on the blockchain. Same as email is ment for sending emails, not downloading website to read them offline. The last piece of of usefulness of the internet is to be able to send value between two peers without anyones permission.
ZoraBora
Several U.S. firms seeking regulatory approval to launch a bitcoin exchange-traded fund (ETF), has estimated that 95 percent of bitcoin trading volumes are faked and only 10 exchanges publish reliable data about volumes on their platforms, without inflated numbers.
Acula
Change is coming.. inevitably. Or rather.. change is inevitable. Agree?
John Accural
I don’t disagree with you entirely but this is literally the driver behind 99% of human behaviour.
You don’t go to university and work your way up the ranks of some shitty job for fun. You’re do it to put yourself, and your family, in a better place financially.
I’ve been involved in blockchain for a while now (coming up on 10 years) and it’s never been about the money. Maybe the ≥2016 influx sees it slightly differently, but that’s inevitable at some stage. Plus you’re only hearing from the 5% who are vocal, and generally snake oil salesmen.
Simon GEE
I think you’re a good storyteller, you should try to write a novel!
John McLean
Thank you for writing this. Hearing non-coders extolling the virtues of blockchain for the past few months has been incredibly frustrating.
TomHarber
I agree with your concerns about relying on Applied Cryptography for security without addressing the human component, but Blockchain’s distributed ledger features has many other useful benefits beyond just security.
ZoraBora
A friend of mine was explaining the idea of smart contracts to me and started with “imagine that you wrote a contract as a bit of code and both people looked at it and were confident that it did was it was supposed to.” I had to stop him there. That hypothetical is absolutely impossible. I do this professionally, and most of my job is figuring out that the code that I thought I understood and tested and checked thoroughly didn’t 100% do what it was supposed to. And that’s without adding in the fact that the person who wrote the code will probably try to hide some behavior I’m not aware of. And this is how everyone is supposed to deal with contracts?
John McLean
Yeah, it’s been weird the past 5 or 6 months because on one side I’m arguing with non-coders who try to attack the technology for uninformed reasons but then I fight the other side of people who think cryptocurrencies are the future. While I disagree with the author’s level of condemnation, it’s nice to actually see well thought out criticism.
John McLean
Hi Norbert, Cyber breaches has highlighted one key area. International Laws have no teeth, because there are no laws written and updated to deal with this. We have countries using cyber breaches for funding and masquerading layers down for ransom. Companies are paying the ransom, because their CEO’s have opted not to strengthen the IT Infrastructure. Entry gates are open. Time for change.
John Accural
I think it’s true that most people are involved in it for the money. But I think the large amounts of money being poured into it is also the source of the overly critical tone of blog posts like that one.
I think if we as programmers were presented with blockchains as a technology solution for the first time today, we would all see the potential that it has for all sorts of problems (it’s the first real world solution to the computer science problem called the Byzantine Generals’ Problem that has we’ve wanted to solve for a long time). But I think everything is clouded currently by the overabundance of hype, the constant talk about cryptocurrencies on financial news outlets and on Wallstreet, with billions of dollars being moved into the space at this very early stage.
I think it is a solution for specific kinds of problems, and it will continue to find the niches where it makes sense. But I also think a lot of the ways they’re trying to use it now won’t work and we’ll find that it isn’t a good solution for many types of problems that are better served with centralized banks and traditional databases.
Tom Jonezz
Bitcoin itself is not replacing ALL TRUST, only trust in the central government issuing money. you can make a “trustful” service on top of it and you can bet that people will prefer that one for the comfort and guarantees it provides. it is just as possible to refund bitcoins , as it is to refund USD (by bitcoin i mean a cheaper/free alternative). The author may be rightfully mad after reading so many “blockchain” bullshit announcements, but that doesn’t justify him making a baseless claim.
how come this has so many upvotes? i know it’s hip to trash cryptos at the moment but maybe try with a better article.
JohnE3
Because Visa takes like a 3% fee on all transactions, you have to get approval to set up a bank account, you need to wait days to transfer money between accounts, your money doesn’t work in every country, and if you live in some countries like Greece, Venezuela or Syria your banking system is completely fucked.
DDonovan
It took thousands of mathematically trained workers years just to roll up census numbers in the early 1900s. This is work a simple spreadsheet program can do in less than a second, being operated by just one person. Technology has been continually replacing certain areas of human labor and making it faster and cheaper, but normally only for processes within businesses.
TommyG
Let’s say I want to build the next Kickstarter. I have to set up a webserver, database server, and something to take credit card payments, make sure I comply with everybody’s terms of service, start a business and pay accountants and lawyers to make sure I won’t get in trouble with all this money I’m handling, etc. Then I have to set fees high enough, do a bunch of marketing, watch my cash flow, make sure the servers keep running, and probably hire people to help.
Or I can write a couple pages of code and post it to a blockchain that supports smart contracts. From then on I don’t have to touch it. I can market it however much I like, but it’s not as stressful because I have no outgoing cashflow. I don’t even have to charge fees. I can forget the whole thing and people can keep using it as long as they like.
Simon GEE
🙂 Love your comment
And99rew
Good article, the point about complexity is key. Blockchain solutions are inherently unable to manage complexity because the functionality of trust and institutions whether corporations or governments is to manage the sheer amount of transactions coming in.
I don’t want to sign, read or be bothered with 500 smart contracts a day, and as Coase has told us 70 years ago, there is no such thing as a perfect contract anyway, because we have to incorporate informal structures and novel events we cannot anticipate in contracts. You cannot write perfect contracts because contracts concern the future, and we can only speculate about, but not know the future. And in case of dispute we need an arbiter and authority or else we’re stuck.
If everything was based on a contract there would be no corporations, there would be no government, there would be no safety regulation, because we’d all be signing bilateral contracts all day, and it would probably take up 90% of our time. Of course, that doesn’t work in large communities so we manage complexity through trusted institutions to which we defer tasks.
The selling point of blockchain technology, that it ditches hierarchies and middlemen is deeply flawed. Because hierarchies and middlemen are extremely useful entities to handle information processing.
TomHarber
What exactly is USD backed with? We’ve been a country for not very long. Look at Zimbabwe and Venezuela they’re currency is essentially useless and the same can happen to our country. The argument goes both ways regardless.
Tom Jonezz
Blockchain technology is evolving as the next big thing, that is now considered for strengthening the “internet of things”. The world is full of devices that are connected to each other, many new devices are being created daily. In 2017, it was estimated that there was around 8.4 billion internet-enabled cameras, thermostats, streetlights and various other electronic products. By the year 2020, this number can exceed 20 billion and by 2030 it could be somewhere around 500 billion or more. New technologies and ideas, are being created daily, in just a few years you will be surrounded by innovation. Currently, all internet devices are made by popular brand names such as, Apple, Google, Samsung and Microsoft; which come with advanced technological systems and marketing incentive to fix all kinds of security problems instantly. But this is not the case for a world with smaller internet enabled devices, such as doorbells, light bulbs, and other simple electronic products. All these devices are made by lesser-known companies. Most of these companies are without sufficient funds to incorporate strong security features. This is where you need to strengthen the internet of things. Insecure devices have already resulted in many cyber-attacks. Blockchain technology is a solution to these problems, as it comes with an advanced way of distributing security software updates. Making Security A Priority In today’s world, all reputed technology companies work hard to ensure that the user is safe, but it’s quite a daunting task. Thousands of complex software packages are taking over the world and can make any system vulnerable to such attacks. These companies have security analysts and researchers who try to fix and identify these flaws before they can cause serious problems. Whenever vulnerabilities are found teams act to send users the updates to fight the problem. Beyond staffing to track problems and provide fixes, such efforts need huge investment. Software needs to respond instantly to automated inquiries and network bandwidth to send updates to millions of users instantly. That is how your iPhone, Microsoft Office, and PlayStations stay seamlessly updated with security fixes. Blockchain Could Be The Future Blockchain is a new technology that is stored in many places at once. It is like a public bulletin board, where individuals can post details of transactions, all these posts are accompanied by digital signatures and can’t be deleted or changed. Experts and researchers from around the world, are suggesting the use of blockchain technology to improve all internet connected device security. Already many networking giants and business groups from around the world have started an initiative to form or develop such system using blockchain technology. Smaller companies need to program all products to check it in the blockchain system periodically; this will help in decreasing any chances of cyber-attacks. Each device needs to have a strong identity, to ensure that the manufacturer is communicating with the right device. This will give confidence to customers that their equipment is efficient and is up to date with security features. All these systems should be easy to program on small devices with limited processing power and memory space. Standard ways of communicating, as well as authenticating updates are necessary. Existing blockchain technology looks promising and it is up to blockchain innovators to continue finding better ways to check the countless numbers of “internet of things” devices for security threats automatically. Importance Of External Pressure Presently, it won’t be enough to develop blockchain based systems which are capable of strengthening smart devices. If manufacturers are not using those systems, all of its products will be at risk to cyber-attacks. Businesses which are making cheap devices with small margins won’t add these layers of protection without assistance or support from outside. Pressure from government regulations and technical assistance is necessary to make the shift from present-day practices.
Zidan78
Perfectly put
Zoeba Jones
It is always about customer experience and value to customer.
Oscar2
Nice. All the best
ZoraBora
QC to the top
CaffD
For anyone that doesn’t want to slog through that poorly written, ad riddled site, here’s an excerpt from the actual papers abstract:
We show that parallel quantum algorithms running in a constant time period are strictly more powerful than their classical counterparts; they are provably better at solving certain linear algebra problems associated with binary quadratic forms. Our work gives an unconditional proof of a computational quantum advantage and simultaneously pinpoints its origin: It is a consequence of quantum nonlocality.
http://science.sciencemag.org/content/362/6412/308
Norbert Biedrzycki
I like your prediction that computers will have an extra quantum processor alongside the normal one to do some very specific routines. I see this implementation being more or less a certainty and much more useful than an quantum only computer.
johnbuzz3
Many well-known blockchain projects are developed from the open-source (free) code — anyone can freely use the source code to develop their own public or private blockchain system. They can do so without needing an application for a license from somebody and paying anything for the use.
John McLean
Decentralized systems are the future. You can’t stuff the genie back in the bottle. Linux was the same way – it starts out crappy, but gets improved over time.
TomK
Great read
John McLean
Blockchain holds multiple advantages over conventional currency and has been hailed by critics and proponents alike as a more efficient way to transfer information. This is due to the unique way that blockchain records transfers on a ledger and thus reduces the possibility of a “double spend”, the idea that a token or unit of currency can be spent more than once. Whilst individual digital wallets or exchanges have been hacked, the problems have been due to poor coding and a lack of awareness of or focus on cyber security. The problems found at SWIFT, a worldwide major financial transaction system, however, are much more alarming. Tens of millions of dollars have been stolen each year from the global financial system since 2015 and this failure comes from the nature of the system relying so heavily on trusted central authorities.
On top politicians have frequently put the interests of the few ahead of the interests of the many or simply been inept at running an economy. As a result, corrupt politicians in places like Venezuela and Zimbabwe have ruined their economies.
Adam Spikey
We should also look at historic transitions. For example,
– 300 years ago 90% or more of all people lived on a farm. Today less than 2% do in developed countries. Have we all stopped eating? No, rather we can all afford to get fat, which is truly a big change in history.
– 100 years ago manufacturing was hard physical work that took many people. Today it takes very few, yet we product many times more goods, because the tools have increased in capability. This has given us all incredible material wealth, historically speaking.
Tesla29
This is an exciting time to combine machine learning with quantum computing. Impressive progress has been made recently in building quantum computers, and quantum machine learning techniques will become powerful tools for finding new patterns in big data.
SimonMcD
I do not agree with opinion about Amazon. I recommend the book “The Four: The Hidden DNA of Amazon, Apple, Facebook, and Google” to better understanding how “Amazon plays”.
TomHarber
it has already happened.
JohnE3
Great topic
John Accural
Computer scientist here. They do exist, Google have one and there’s another famous one which can be purchased (for crazy sums of money) called D-wave. They are not quantum computers in their final form, but they do work, sort of. I won’t go into the details of why I say “sort of”. We also know what they will be capable of because we can do the calculations. But we can know to a relatively high degree of certainty.
SimonMcD
Would Quantum computers be able to very quickly generate and check seeds for presence of any IOTAs and perform an attack in that way?
They could, but it wouldn’t get them anywhere. let’s say there was a quantum computer with absolutely ridiculous power and bandwidth that could generate and check the balance of one billion seeds per second. let’s say everyone on earth had one of these computers, and they had all been running since the time the earth was formed. as of now, all those computers would have checked the balance of 0.00000000000000000000000000000000000000000000000000000000000000000000000000000001% of all possible seeds.
Zoeba Jones
[(10^9) seeds per second] * [(7*10^9) humans on earth]*[3600 seconds per hour]*[24 hours per day]*[365.25 days per year]*[4.5*10^9 years since Earth was formed] / [27^81 possible seeds]
it’s rough napkin math and i might be off by 1 or 2 zeros in the percentage since I was just mashing the 0 key on my phone but it at least gives a good idea of how unlikely not just a specific seed, but any seed with a balance is to be guessed at random.
Adam T
Seriously?
Zidan78
Apples and Oranges my friend – transistors do not need to be near absolute zero to operate, nor are they subject to time based decoherance (among MANY other differences). On a similar theme, Moore’s law effectively ended for silicon when Apple reached 10nM manufacturing standards, meaning that trace widths are ~ tens of copper atoms wide.
John McLean
Many people have stopped trusting governments (if you believe that anyone trusted them in the first place). Politicians have frequently put the interests of the few ahead of the interests of the many or simply been inept at running an economy. As a result, corrupt politicians in places like Venezuela and Zimbabwe have ruined their economies.
Check Batin
Great article. Thank you for sharing
Norbert Biedrzycki
Thank you
TomCat
It’s ~50%, and after one use, it’s 128 bit security, which is equivalent to Bitcoin’s security. It’s statistically possible for it to be higher or lower. https://iota.stackexchange.com/questions/245/what-information-is-leaked-if-i-reuse-an-address
I guess you are insinuating that this is a bad tradeoff for quantum security? If so, I’d like to point out that wallets can be automated to deal with the issue and permanent address solutions are being created, so it’s a temporary inconvenience for a long term security measure. My guess is other coins will have to find solutions once quantum computers come online, and unless they have a plan in place and tested, they won’t have much time in which to work–as we are seeing with BLT it may have effects on other parts of coin design, so kicking the can down the road in hopes that quantum computers are a distant problem may not be the wiser option.
ZoraBora
🙂
Tom Jonezz
Do we need those? If you want to store data in a robust way, we solved that problem with off-site data centers, back-ups, and databases running on servers that are owned or rented by the company using them. What possible advantage does blockchain have over a system that is so robust every major company and website uses by moving it out of a data center that they control over to random internet users? We’re even at the point that we have blockchain database companies which are putting all of the ‘distrubuted’ computers that they own under a single roof.
AdaZombie
Reclame process was not caused by address reused, but in a bug that allow to bruteforce some addresses without “address reused”. If you send twice from an address 50% of your private key is revealed but this was not the problem caused by the bug. The bug was solved. Correct me if I misunderstood something
Tom299
And did you know that due to quantum computer secure signatures it leaks 50% of your private key when doing a transaction? This is the reason address reuse is not allowed.
tom lee
Scientists May Have Found a Way to Combat Quantum Computer Blockchain Hacking – The principle is based on Zero-knowledge proofs which allow you to validate information without sharing it.
https://beta.ourmedian.com/files/1523/consensus—immutable-agreement-for-the-internet-of-value
TomaszKik
It’s time for a trusted application of this technology
Adam Spark Two
Well, from 5 qubits in 2016, to 50 in 2017, to 72 in beginning 2018. That’s a pretty steep curve. Lot’s of other things to improve, it won’t be there tomorrow, but the development is speeding up. Budgeds grow with the development. IBM, Google, Intel, Microsoft and other specialized companies etc are in on this.
https://www.technologyreview.com/s/603495/10-breakthrough-technologies-2017-practical-quantum-computers/ “And a million-physical-qubit system, whose general computing applications are still difficult to even fathom? It’s conceivable, says Neven, “on the inside of 10 years.” ” (That is Harmut Neven the head of Google’s quantum computing effort)
https://www.research.ibm.com/5-in-5/quantum-computing/ IBM believes quantum computers will be mainstream in 5 years. (Meaning outside of research labs, but not necessarily in livingrooms of the average Joe. And no ammount of qubits mentioned though)
AdaZombie
Reclame process was not caused by address reused, but in a bug that allow to bruteforce some addresses without “address reused”. If you send twice from an address 50% of your private key is revealed but this was not the problem caused by the bug. The bug was solved. Correct me if I misunderstood something
PiotrPawlow
Financial global system – here I come 🙂
Oscar2
scary
John McLean
It’s a bit like if everyone suddenly started getting really excited about how “chicken soup is going to change the face of the construction industry forever”. It’s literally nonsense: chicken soup doesn’t solve construction issues. Blockchains don’t solve the issues that it is being applied to, in many cases.
A blockchain is a datastructure that does a very specific thing. Most people who talk about applying blockchains for things have subtly misunderstood that thing, so their proposals don’t actually make sense. This is leading to a very expensive, very slow-motion technical train crash.
Tom Jonezz
Personally I’ll be happy to see bitcoin die, not because i think the idea of cryto currencies are bad idea, but because bitcoin is using the electricity of a small country and massively driving up hardware prices for something almost no one is actually using as a currency anyway. It’s just been an enormous speculative bubble. The idea that bitcoin has value because the coins are limited doesn’t really work, because people can create unlimited branches off bitcoin, and you have already seen this with all the different crypto currencies that have been created.
Mac McFisher
Bitcoin has in the past added new transaction/signature formats with soft forks. So that’s not so difficult. What’s nearly impossible is retiring old ones. Even if Bitcoin updates, there will be lots of bitcoins in unsecured addresses. At first reused addresses will be attacked, then eventually there may be double spend attacks. This is bad for the whole ecosystem. Even if bitcoins are only taken from lost wallets or deceased people, it creates an inflationary effect.
DDonovan
Money is arguably one of humanity’s most important inventions. From beaver pelts to gold bars, the form and function of money has constantly fluctuated throughout history. In the modern world, the definition of money is blurrier than ever. Central banks have opted to create trillions of dollars of currency out of thin air since the financial crisis – and on the flipside, you can actually use blockchain technology to create your own competing cryptocurrency in just a few clicks. Regardless of what is money and what is not, people are borrowing record amounts of it.
John McLean
It’s a bit like if everyone suddenly started getting really excited about how “chicken soup is going to change the face of the construction industry forever”. It’s literally nonsense: chicken soup doesn’t solve construction issues. Blockchains don’t solve the issues that it is being applied to, in many cases.
A blockchain is a datastructure that does a very specific thing. Most people who talk about applying blockchains for things have subtly misunderstood that thing, so their proposals don’t actually make sense. This is leading to a very expensive, very slow-motion technical train crash.
Jack666
The possible existence of quantum computers used to be vague and purely theoretical.
Now it’s starts to be the other way around, quantum computers develop fast, and existing blockchains only have vaugue plans to be quantum resistant. Blockchains who had concrete plans to become quantum resistant have been shown to be wrong. BTC can’t agree on how to improve speed, it will take way longer to fork to quantum resistant keys. You see in the paper above they are vulnerable to quantum attacks. You see they need to fork to improve. It will affect their performance.
The only way is to start from scratch and improve over the years
Simon GEE
Thank you. I’ve been thinking about this for a while. How do you feel it’ll affect current systems using blockchain technology, such as Bitcoin. Won’t all cryptocurrencies lose value as people realize they can be broken easily? I’m just looking forward to the quantum web and quantum crypto.
ZoraBora
What I’d like to see is a quantum-powered Proof of Work algorithm. Look what PoW has done for the cryptocurrency “mining” industry – it has increased efficiency by at least 10,000x by going from CPUs at first to GPUs, FPGAs, and finally ASICs.
If cryptocurrencies would adopt mining powered by quantum computers, that would create a race for who designs and builds the most powerful quantum computer, which would be great for the rest of us, too.
First off, it would give us more powerful quantum computers faster. Second, the quantum computers’ mining algorithm could be something like simulations of molecule interactions. What I’m saying is that these mining rigs could be used directly to help science discoveries.
ZoraBora
QRL has done it, they are in the external audit fase now where two external firms do the audit. There will be a bug bounty program as well: https://medium.com/the-quantum-resistant-ledger/external-audits-bug-bounties-439db9c94fd2
ZoraBora
If quantum computers threaten blockchains, quantum blockchains could be the defense
https://www.technologyreview.com/s/611022/if-quantum-computers-threaten-blockchains-quantum-blockchains-could-be-the-defense/
Oscar2
We see more applications of blockchain in public sector and central government
TomK
In my opinion the lack of trust is caused by lack of knowledge.
Adam Spikey
Great read and I agree, we are on at the dawn of the new “internet.” Blockchain technology provides accountability, transparency, and traceability for the value chain of a company and its supply chain processes and more. Some of the commodities industry understand the value gained by having accountability for their business units by use of blockchain technologies. De Beers used their blockchain platform, TRACR, successfully for their diamonds. Goldcorp is not far behind utilizing a blockchain platform, Tradewind.
Eventually, more successes with these blockchain platforms will be commonplace for all commodities, not just precious metals. Blockchain technology can move on to most industries and sectors from lumber to automotive.
Tom Jonezz
Smart contracts are perhaps the most important feature of the Digital Ledger technology pioneered originally by the Ethereum platform and has now gained wider acceptance & incorporation in the upcoming projects. These contracts let you exchange any two assets on a secure & transparent network without an intermediary.
TomaszK1
Great piece! In my experience when talking to skeptics about blockchain, they seem to point out the lack of actual project use cases. Sure their are a lot of use cases that could affect many different industries but how do we get the masses to believe in the trust protocol and immutable ledger? In my opinion, enterprise permissioned ledgers would be the best way to build up the trust and show people the true power of the technology and the trust protocol.
Norbert Biedrzycki
🙂
John McLean
The potential of cryptocurrencies and crypto-assets is really huge. There is a place for new type of comprehensive financial institutions based on blockchain
Karel Doomm2
Gonna put voting on the blockchain? Great. How much energy are you going to waste to secure this block chain? Cause corporations or wealthy individuals would never use their wealth to affect the outcome of an election. Last presidential elections spent something like $7 billion. If someone could just get a bunch of servers and do a 51% attack for like $500 million dollars, it would be a good investment. Also, keep in mind, other nation states never interfere with elections….
So you need to probably burn a billion dollars worth of energy just to secure the election. Something like that. Maybe more if China wants to pick the next U.S. president.
TomaszK1
Norbert, good that you separate Blockchain and Crypto…but the bottom line is that we just don’t know how secure it is, except in theory, right? And doubly so given the potential rise of quantum computing?
Norbert
It is an endless war in between sword and a shield 🙂
Oscar2
… and who is gonna win?
Adam T
.. we the people
Karel Doomm2
The wasted resources used to process a block in the blockchain must be a good sized fraction of the value of the transactions that occur in an average block. If the wasted resources were double the value of the transactions in an average block, a 51% attack would never be profitable. But burning twice as much resources as you are transacting would be insane. Burning an 1:1 ratio of resources to transaction value is insane also. So the amount of wasted resources will be below this number. However, the lower it goes, the more profitable and more likely a 51% attack becomes. If someone can just spool up a bunch of cloud servers and perform a 51% attack, it’s probably gonna happen.
So if you are using blockchain to record things like real estate, then you must waste several houses worth of resources per block, PER BLOCK, to secure each block or else a 51% attack is inevitable. So imagine burning a million dollars worth of coal each block.
TomHarber
The integrity of public blockchains for crypto-currency has made it a “futuristic integrity wand” to be waved at every problem. Except blockchain doesn’t even solve most problems of trust. The integrity of data on a public blockchain can be trusted not to change, but that says nothing about whether the data is right in the first place. […] Not for nothing do so many blockchain start-up pitches focus on the technology, as if it were inherently better to bring blockchain to x , rather than leading with the solution to a real-world problem. They are tokens in search of users as an end in itself.
TomHarber
And the article https://ftalphaville.ft.com/2018/04/13/1523592006000/Sell-all-crypto-and-abandon-all-blockchain/
TomHarber
Blockchain does nothing that money and a bank doesn’t do now. Here is a damning article from the FT.
TonyHor
Great article. Thank you for publishing
Adam T
very correct
TommyG
Because it creates a permanent record of anything you desire over time, a record that no one can change. You can interact with it, search through it and add your own records to it. It can be used for all kinds of recording and archiving: legal, financial, government, education, and anything else you can think of.